The concerns surrounding the reliability and security of Tesla’s vehicles have been further fanned after two security researchers explained how they successfully accessed unattended and stationary Tesla cars.
The two researchers, Ralf-Philipp Weinmann of Kunnamon Inc and Benedikt Schmotzle of Comsecuris GmbH, used a vulnerability in Tesla’s system found in an open-source software component.
The analysis and findings of the research were published on May 4 and included details on the exact methodology the two researchers deployed, which involved the use of a drone.
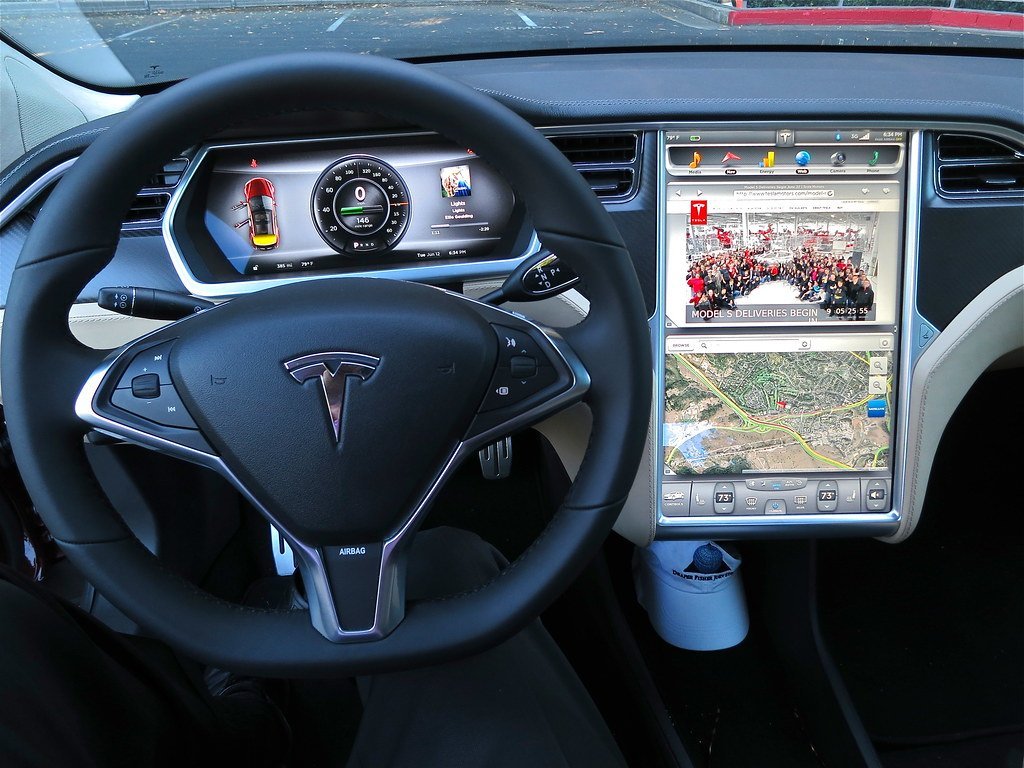
The drone allowed the pair to control the vehicles’ infotainment systems over a wireless network.
Moreover, the researchers were also able to manipulate the vehicle’s doors, boot, the positioning of the seats, as well change the software modes governing its electrical steering and acceleration style.
The amount of control gained over the vehicle stopped short of being able to drive the car remotely and essentially mirrored a driver’s ability to press the buttons within the cabin outside of engaging driving mode.
“Looking at the fact TBONE required no user interaction, and ease of delivery of the payload to parked cars, we felt this attack was ‘wormable’ and could have been weaponised,” said Weinmann.
“Adding a privilege escalation exploit such as CVE-2021-3347 to TBONE would allow us to load new Wi-Fi firmware in the Tesla car, turning it into an access point which could be used to exploit other Tesla cars that come into the victim car’s proximity. We did not want to weaponise this exploit into a worm, however,” Weinmann added.
The exploitable components used to demonstrate the system’s vulnerability were not exclusively used on Tesla vehicles, but have also been implemented in the systems of other car manufacturers.
One of the key reasons this remote zero-click security exploit has been exhibited in public and detailed in the published report is that it has since been remedied through the deployment of specific security patches which have resolved the issue.






Click here to change your cookie preferences